Search Results for author: Ricardo Violato
Found 1 papers, 0 papers with code
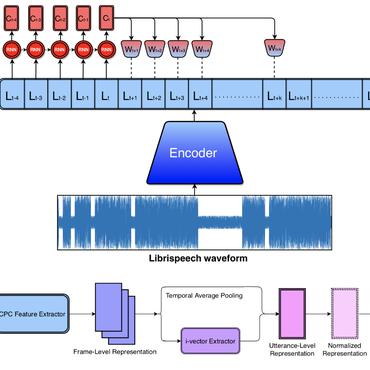
Using Deep Learning for Detecting Spoofing Attacks on Speech Signals
no code implementations • 7 Aug 2015 • Alan Godoy, Flávio Simões, José Augusto Stuchi, Marcus de Assis Angeloni, Mário Uliani, Ricardo Violato
It is well known that speaker verification systems are subject to spoofing attacks.