Search Results for author: Menghao Li
Found 7 papers, 2 papers with code
Deep Linear Array Pushbroom Image Restoration: A Degradation Pipeline and Jitter-Aware Restoration Network
1 code implementation • 16 Jan 2024 • Zida Chen, Ziran Zhang, Haoying Li, Menghao Li, Yueting Chen, Qi Li, Huajun Feng, Zhihai Xu, Shiqi Chen
Both the proposed JARNet and LAP image synthesis pipeline establish a foundation for addressing this intricate challenge.
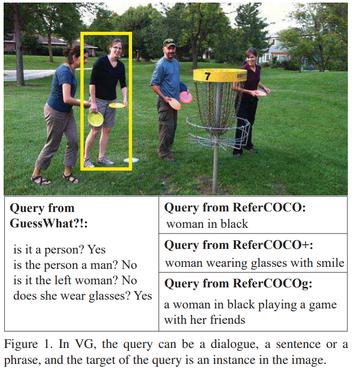
Iterative Robust Visual Grounding with Masked Reference based Centerpoint Supervision
1 code implementation • 23 Jul 2023 • Menghao Li, Chunlei Wang, Wenquan Feng, Shuchang Lyu, Guangliang Cheng, Xiangtai Li, Binghao Liu, Qi Zhao
The proposed framework is evaluated on five regular VG datasets and two newly constructed robust VG datasets.
Mobile Image Restoration via Prior Quantization
no code implementations • 10 May 2023 • Shiqi Chen, Jinwen Zhou, Menghao Li, Yueting Chen, Tingting Jiang
In digital images, the performance of optical aberration is a multivariate degradation, where the spectral of the scene, the lens imperfections, and the field of view together contribute to the results.
Look in Different Views: Multi-Scheme Regression Guided Cell Instance Segmentation
no code implementations • 17 Aug 2022 • Menghao Li, Wenquan Feng, Shuchang Lyu, Lijiang Chen, Qi Zhao
On the DSB2018 and CA2. 5, our network surpasses previous methods by 1. 2% (AP50).
DynaTune: Dynamic Tensor Program Optimization in Deep Neural Network Compilation
no code implementations • ICLR 2021 • Minjia Zhang, Menghao Li, Chi Wang, Mingqin Li
Recently, the DL compiler, together with Learning to Compile has proven to be a powerful technique for optimizing deep learning models.
AdaTune: Adaptive Tensor Program Compilation Made Efficient
no code implementations • NeurIPS 2020 • Menghao Li, Minjia Zhang, Chi Wang, Mingqin Li
Deep learning models are computationally intense, and implementations often have to be highly optimized by experts or hardware vendors to be usable in practice.
Understanding Android Obfuscation Techniques: A Large-Scale Investigation in the Wild
no code implementations • 5 Jan 2018 • Shuaike Dong, Menghao Li, Wenrui Diao, Xiangyu Liu, Jian Liu, Zhou Li, Fenghao Xu, Kai Chen, Xiao-Feng Wang, Kehuan Zhang
In this paper, we seek to better understand Android obfuscation and depict a holistic view of the usage of obfuscation through a large-scale investigation in the wild.
Cryptography and Security