Search Results for author: Mashrur Chowdhury
Found 24 papers, 1 papers with code
An Overview of Automated Vehicle Platooning Strategies
no code implementations • 8 Mar 2024 • M Sabbir Salek, Mugdha Basu Thakur, Pardha Sai Krishna Ala, Mashrur Chowdhury, Matthias Schmid, Pamela Murray-Tuite, Sakib Mahmud Khan, Venkat Krovi
Automated vehicle (AV) platooning has the potential to improve the safety, operational, and energy efficiency of surface transportation systems by limiting or eliminating human involvement in the driving tasks.
AR-GAN: Generative Adversarial Network-Based Defense Method Against Adversarial Attacks on the Traffic Sign Classification System of Autonomous Vehicles
no code implementations • 31 Dec 2023 • M Sabbir Salek, Abdullah Al Mamun, Mashrur Chowdhury
The novelty of the AR-GAN lies in (i) assuming zero knowledge of adversarial attack models and samples and (ii) providing consistently high traffic sign classification performance under various adversarial attack types.
Development and Evaluation of Ensemble Learning-based Environmental Methane Detection and Intensity Prediction Models
no code implementations • 18 Dec 2023 • Reek Majumder, Jacquan Pollard, M Sabbir Salek, David Werth, Gurcan Comert, Adrian Gale, Sakib Mahmud Khan, Samuel Darko, Mashrur Chowdhury
The environmental impacts of global warming driven by methane (CH4) emissions have catalyzed significant research initiatives in developing novel technologies that enable proactive and rapid detection of CH4.
A Hybrid Defense Method against Adversarial Attacks on Traffic Sign Classifiers in Autonomous Vehicles
no code implementations • 25 Apr 2022 • Zadid Khan, Mashrur Chowdhury, Sakib Mahmud Khan
Moreover, the hybrid defense method, presented in this study, improves the accuracy for traffic sign classification compared to the traditional defense methods (i. e., JPEG filtering, feature squeezing, binary filtering, and random filtering) up to 6%, 50%, and 55% for FGSM, MIM, and PGD attacks, respectively.
Theoretical Development and Numerical Validation of an Asymmetric Linear Bilateral Control Model- Case Study for an Automated Truck Platoon
no code implementations • 29 Dec 2021 • M Sabbir Salek, Mashrur Chowdhury, Mizanur Rahman, Kakan Dey, Md Rafiul Islam
The novelty of the asymmetric LBCM is that using this model all the follower vehicles in a platoon can adjust their acceleration and deceleration to closely follow a constant desired time gap to improve platoon operational efficiency while maintaining local and string stability.
Hybrid Quantum-Classical Neural Network for Cloud-supported In-Vehicle Cyberattack Detection
no code implementations • 14 Oct 2021 • Mhafuzul Islam, Mashrur Chowdhury, Zadid Khan, Sakib Mahmud Khan
A classical computer works with ones and zeros, whereas a quantum computer uses ones, zeros, and superpositions of ones and zeros, which enables quantum computers to perform a vast number of calculations simultaneously compared to classical computers.
A Sensor Fusion-based GNSS Spoofing Attack Detection Framework for Autonomous Vehicles
no code implementations • 19 Aug 2021 • Sagar Dasgupta, Mizanur Rahman, Mhafuzul Islam, Mashrur Chowdhury
Data from multiple low-cost in-vehicle sensors (i. e., accelerometer, steering angle sensor, speed sensor, and GNSS) are fused and fed into a recurrent neural network model, which is a long short-term memory (LSTM) network for predicting the location shift, i. e., the distance that an AV travels between two consecutive timestamps.
Hybrid Quantum-Classical Neural Network for Incident Detection
no code implementations • 2 Aug 2021 • Zadid Khan, Sakib Mahmud Khan, Jean Michel Tine, Ayse Turhan Comert, Diamon Rice, Gurcan Comert, Dimitra Michalaka, Judith Mwakalonge, Reek Majumdar, Mashrur Chowdhury
The incident detection performance of the hybrid model is evaluated against baseline classical ML models.
Efficacy of Statistical and Artificial Intelligence-based False Information Cyberattack Detection Models for Connected Vehicles
no code implementations • 2 Aug 2021 • Sakib Mahmud Khan, Gurcan Comert, Mashrur Chowdhury
Change point models, can be used for real-time anomaly detection caused by the false information attack.
Hybrid Classical-Quantum Deep Learning Models for Autonomous Vehicle Traffic Image Classification Under Adversarial Attack
no code implementations • 2 Aug 2021 • Reek Majumder, Sakib Mahmud Khan, Fahim Ahmed, Zadid Khan, Frank Ngeni, Gurcan Comert, Judith Mwakalonge, Dimitra Michalaka, Mashrur Chowdhury
To make classification models resilient against adversarial attacks, we used a hybrid deep-learning model with both the quantum and classical layers.
Sensor Fusion-based GNSS Spoofing Attack Detection Framework for Autonomous Vehicles
no code implementations • 5 Jun 2021 • Sagar Dasgupta, Mizanur Rahman, Mhafuzul Islam, Mashrur Chowdhury
In this study, a sensor fusion based GNSS spoofing attack detection framework is presented that consists of three concurrent strategies for an autonomous vehicle (AV): (i) prediction of location shift, (ii) detection of turns (left or right), and (iii) recognition of motion state (including standstill state).
Assessment of System-Level Cyber Attack Vulnerability for Connected and Autonomous Vehicles Using Bayesian Networks
no code implementations • 18 Nov 2020 • Gurcan Comert, Mashrur Chowdhury, David M. Nicol
This study presents a methodology to quantify vulnerability of cyber attacks and their impacts based on probabilistic graphical models for intelligent transportation systems under connected and autonomous vehicles framework.
Prediction-Based GNSS Spoofing Attack Detection for Autonomous Vehicles
no code implementations • 16 Oct 2020 • Sagar Dasgupta, Mizanur Rahman, Mhafuzul Islam, Mashrur Chowdhury
A spoofed attack is difficult to detect as a spoofer (attacker who performs spoofing attack) can mimic the GNSS signal and transmit inaccurate location coordinates to an AV.
Change Point Models for Real-time Cyber Attack Detection in Connected Vehicle Environment
no code implementations • 5 Mar 2020 • Gurcan Comert, Mizanur Rahman, Mhafuzul Islam, Mashrur Chowdhury
Connected vehicle (CV) systems are cognizant of potential cyber attacks because of increasing connectivity between its different components such as vehicles, roadside infrastructure, and traffic management centers.
Dynamic Error-bounded Lossy Compression (EBLC) to Reduce the Bandwidth Requirement for Real-time Vision-based Pedestrian Safety Applications
no code implementations • 29 Jan 2020 • Mizanur Rahman, Mhafuzul Islam, Jon C. Calhoun, Mashrur Chowdhury
The objective of this study is to develop a real-time error-bounded lossy compression (EBLC) strategy to dynamically change the video compression level depending on different environmental conditions in order to maintain a high pedestrian detection accuracy.
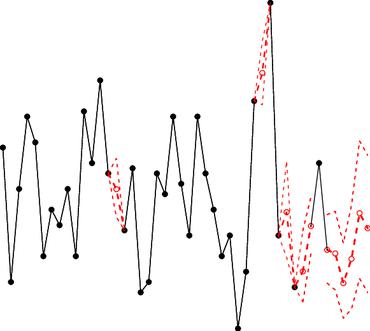
Grey Models for Short-Term Queue Length Predictions for Adaptive Traffic Signal Control
no code implementations • 29 Dec 2019 • Gurcan Comert, Zadid Khan, Mizanur Rahman, Mashrur Chowdhury
Thus, the objective of this study is to develop queue length prediction models for signalized intersections that can be leveraged by ASCS using four variations of Grey systems: (i) the first order single variable Grey model (GM(1, 1)); (ii) GM(1, 1) with Fourier error corrections; (iii) the Grey Verhulst model (GVM), and (iv) GVM with Fourier error corrections.
Vision-based Pedestrian Alert Safety System (PASS) for Signalized Intersections
no code implementations • 2 Jul 2019 • Mhafuzul Islam, Mizanur Rahman, Mashrur Chowdhury, Gurcan Comert, Eshaa Deepak Sood, Amy Apon
The contribution of this paper lies in the development of a system using a vision-based deep learning model that is able to generate personal safety messages (PSMs) in real-time (every 100 milliseconds).
Long Short-Term Memory Neural Networks for False Information Attack Detection in Software-Defined In-Vehicle Network
no code implementations • 24 Jun 2019 • Zadid Khan, Mashrur Chowdhury, Mhafuzul Islam, Chin-Ya Huang, Mizanur Rahman
This attack detection model can detect false information with an accuracy, precision and recall of 95%, 95% and 87%, respectively, while satisfying the real-time communication and computational requirements.
Connected Vehicle Application Development Platform (CVDeP) for Edge-centric Cyber-Physical Systems
1 code implementation • 2 Dec 2018 • Mhafuzul Islam, Mizanur Rahman, Sakib Mahmud Khan, Mashrur Chowdhury, Lipika Deka
Connected vehicle (CV) application developers need a development platform to build, test and debug CV applications, such as safety, mobility, and environmental applications, in an edge-centric Cyber-Physical Systems.
Networking and Internet Architecture
Change Point Models for Real-time V2I Cyber Attack Detection in a Connected Vehicle Environment
no code implementations • 30 Nov 2018 • Gurcan Comert, Mizanur Rahman, Mhafuzul Islam, Mashrur Chowdhury
Connected vehicle (CV) systems are cognizant of potential cyber attacks because of increasing connectivity between its different components such as vehicles, roadside infrastructure and traffic management centers.
Cryptography and Security
Real time Traffic Flow Parameters Prediction with Basic Safety Messages at Low Penetration of Connected Vehicles
no code implementations • 8 Nov 2018 • Mizanur Rahman, Mashrur Chowdhury, Jerome McClendon
This estimated traffic flow parameters from low penetration of connected vehicles become noisy compared to 100 percent penetration of CVs, and such noise reduces the real time prediction accuracy of a machine learning model, such as the accuracy of long short term memory (LSTM) model in terms of predicting traffic flow parameters.
Real-time Pedestrian Detection Approach with an Efficient Data Communication Bandwidth Strategy
no code implementations • 27 Aug 2018 • Mizanur Rahman, Mhafuzul Islam, Jon Calhoun, Mashrur Chowdhury
We utilize a lossy compression technique on traffic camera data to determine the tradeoff between the reduction of the communication bandwidth requirements and a defined object detection accuracy.
Development and Evaluation of Recurrent Neural Network based Models for Hourly Traffic Volume and AADT Prediction
no code implementations • 15 Aug 2018 • MD Zadid Khan, Sakib Mahmud Khan, Mashrur Chowdhury, Kakan Dey
The analysis indicates that the LSTM model performs better than simple RNN and GRU models, and imputation performs better than masking to predict future traffic volume.
Development of Statewide AADT Estimation Model from Short-Term Counts: A Comparative Study for South Carolina
no code implementations • 30 Nov 2017 • Sakib Mahmud Khan, Sababa Islam, MD Zadid Khan, Kakan Dey, Mashrur Chowdhury, Nathan Huynh
SVR models are validated for each roadway functional class using the 2016 ATR data and selected short-term count data collected by the South Carolina Department of Transportation (SCDOT).