Search Results for author: Leo Tsourides
Found 1 papers, 0 papers with code
Detecting and Quantifying Malicious Activity with Simulation-based Inference
no code implementations • 6 Oct 2021 • Andrew Gambardella, Bogdan State, Naeemullah Khan, Leo Tsourides, Philip H. S. Torr, Atılım Güneş Baydin
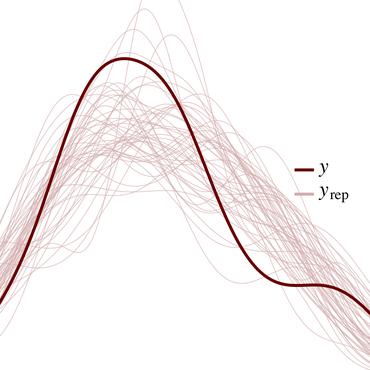
We propose the use of probabilistic programming techniques to tackle the malicious user identification problem in a recommendation algorithm.