Search Results for author: Kim Hammar
Found 12 papers, 9 papers with code
Intrusion Tolerance for Networked Systems through Two-Level Feedback Control
no code implementations • 2 Apr 2024 • Kim Hammar, Rolf Stadler
We formulate intrusion tolerance for a system with service replicas as a two-level optimal control problem.
Conjectural Online Learning with First-order Beliefs in Asymmetric Information Stochastic Games
no code implementations • 29 Feb 2024 • Tao Li, Kim Hammar, Rolf Stadler, Quanyan Zhu
To address these limitations, we propose conjectural online learning (\textsc{col}), an online method for generic \textsc{aisg}s. \textsc{col} uses a forecaster-actor-critic (\textsc{fac}) architecture where subjective forecasts are used to conjecture the opponents' strategies within a lookahead horizon, and Bayesian learning is used to calibrate the conjectures.
Automated Security Response through Online Learning with Adaptive Conjectures
1 code implementation • 19 Feb 2024 • Kim Hammar, Tao Li, Rolf Stadler, Quanyan Zhu
We study automated security response for an IT infrastructure and formulate the interaction between an attacker and a defender as a partially observed, non-stationary game.
Scalable Learning of Intrusion Responses through Recursive Decomposition
1 code implementation • 6 Sep 2023 • Kim Hammar, Rolf Stadler
We study automated intrusion response for an IT infrastructure and formulate the interaction between an attacker and a defender as a partially observed stochastic game.
Optimal Observation-Intervention Trade-Off in Optimisation Problems with Causal Structure
no code implementations • 5 Sep 2023 • Kim Hammar, Neil Dhir
We give theoretical results detailing the structure of the optimal stopping times and demonstrate the generality of our approach by showing that it can be integrated with existing causal Bayesian optimisation algorithms.
Learning Near-Optimal Intrusion Responses Against Dynamic Attackers
1 code implementation • 11 Jan 2023 • Kim Hammar, Rolf Stadler
We study automated intrusion response and formulate the interaction between an attacker and a defender as an optimal stopping game where attack and defense strategies evolve through reinforcement learning and self-play.
Learning Security Strategies through Game Play and Optimal Stopping
1 code implementation • 29 May 2022 • Kim Hammar, Rolf Stadler
We study automated intrusion prevention using reinforcement learning.
A System for Interactive Examination of Learned Security Policies
1 code implementation • 3 Apr 2022 • Kim Hammar, Rolf Stadler
We present a system for interactive examination of learned security policies.
Intrusion Prevention through Optimal Stopping
2 code implementations • 30 Oct 2021 • Kim Hammar, Rolf Stadler
We therefore develop a reinforcement learning approach to approximate an optimal threshold policy.
Learning Intrusion Prevention Policies through Optimal Stopping
1 code implementation • 14 Jun 2021 • Kim Hammar, Rolf Stadler
We study automated intrusion prevention using reinforcement learning.
Finding Effective Security Strategies through Reinforcement Learning and Self-Play
1 code implementation • 17 Sep 2020 • Kim Hammar, Rolf Stadler
We present a method to automatically find security strategies for the use case of intrusion prevention.
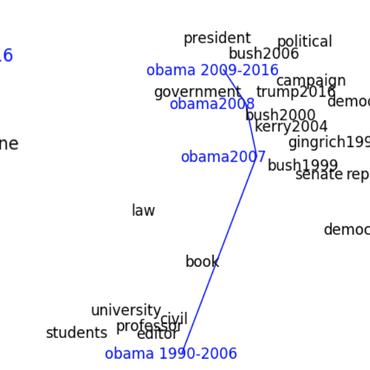
Deep Text Mining of Instagram Data Without Strong Supervision
1 code implementation • 24 Sep 2019 • Kim Hammar, Shatha Jaradat, Nima Dokoohaki, Mihhail Matskin
In this paper, we present methods for unsupervised mining of fashion attributes from Instagram text, which can enable a new kind of user recommendation in the fashion domain.