Search Results for author: Kien Do
Found 26 papers, 10 papers with code
Variational Flow Models: Flowing in Your Style
no code implementations • 5 Feb 2024 • Kien Do, Duc Kieu, Toan Nguyen, Dang Nguyen, Hung Le, Dung Nguyen, Thin Nguyen
We introduce "posterior flows" - generalizations of "probability flows" to a broader class of stochastic processes not necessarily diffusion processes - and propose a systematic training-free method to transform the posterior flow of a "linear" stochastic process characterized by the equation Xt = at * X0 + st * X1 into a straight constant-speed (SC) flow, reminiscent of Rectified Flow.
Revisiting the Dataset Bias Problem from a Statistical Perspective
no code implementations • 5 Feb 2024 • Kien Do, Dung Nguyen, Hung Le, Thao Le, Dang Nguyen, Haripriya Harikumar, Truyen Tran, Santu Rana, Svetha Venkatesh
To overcome this challenge, we propose to approximate \frac{1}{p(u|b)} using a biased classifier trained with "bias amplification" losses.
Domain Generalisation via Risk Distribution Matching
1 code implementation • 28 Oct 2023 • Toan Nguyen, Kien Do, Bao Duong, Thin Nguyen
Hence, we propose a compelling proposition: Minimising the divergences between risk distributions across training domains leads to robust invariance for DG.
Beyond Surprise: Improving Exploration Through Surprise Novelty
1 code implementation • 9 Aug 2023 • Hung Le, Kien Do, Dung Nguyen, Svetha Venkatesh
We present a new computing model for intrinsic rewards in reinforcement learning that addresses the limitations of existing surprise-driven explorations.
Memory-Augmented Theory of Mind Network
no code implementations • 17 Jan 2023 • Dung Nguyen, Phuoc Nguyen, Hung Le, Kien Do, Svetha Venkatesh, Truyen Tran
Social reasoning necessitates the capacity of theory of mind (ToM), the ability to contextualise and attribute mental states to others without having access to their internal cognitive structure.
Causal Inference via Style Transfer for Out-of-distribution Generalisation
1 code implementation • 6 Dec 2022 • Toan Nguyen, Kien Do, Duc Thanh Nguyen, Bao Duong, Thin Nguyen
A well-known existing causal inference method like back-door adjustment cannot be applied to remove spurious correlations as it requires the observation of confounders.
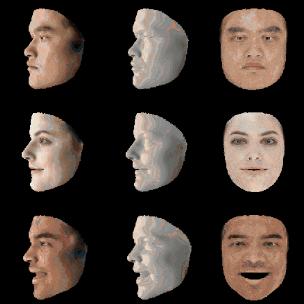
Face Swapping as A Simple Arithmetic Operation
1 code implementation • 19 Nov 2022 • Truong Vu, Kien Do, Khang Nguyen, Khoat Than
We propose a novel high-fidelity face swapping method called "Arithmetic Face Swapping" (AFS) that explicitly disentangles the intermediate latent space W+ of a pretrained StyleGAN into the "identity" and "style" subspaces so that a latent code in W+ is the sum of an "identity" code and a "style" code in the corresponding subspaces.
Momentum Adversarial Distillation: Handling Large Distribution Shifts in Data-Free Knowledge Distillation
no code implementations • 21 Sep 2022 • Kien Do, Hung Le, Dung Nguyen, Dang Nguyen, Haripriya Harikumar, Truyen Tran, Santu Rana, Svetha Venkatesh
Since the EMA generator can be considered as an ensemble of the generator's old versions and often undergoes a smaller change in updates compared to the generator, training on its synthetic samples can help the student recall the past knowledge and prevent the student from adapting too quickly to new updates of the generator.
Black-box Few-shot Knowledge Distillation
1 code implementation • 25 Jul 2022 • Dang Nguyen, Sunil Gupta, Kien Do, Svetha Venkatesh
Traditional KD methods require lots of labeled training samples and a white-box teacher (parameters are accessible) to train a good student.
Defense Against Multi-target Trojan Attacks
no code implementations • 8 Jul 2022 • Haripriya Harikumar, Santu Rana, Kien Do, Sunil Gupta, Wei Zong, Willy Susilo, Svetha Venkastesh
To defend against this attack, we first introduce a trigger reverse-engineering mechanism that uses multiple images to recover a variety of potential triggers.
Learning to Constrain Policy Optimization with Virtual Trust Region
no code implementations • 20 Apr 2022 • Hung Le, Thommen Karimpanal George, Majid Abdolshah, Dung Nguyen, Kien Do, Sunil Gupta, Svetha Venkatesh
We introduce a constrained optimization method for policy gradient reinforcement learning, which uses a virtual trust region to regulate each policy update.
Learning Theory of Mind via Dynamic Traits Attribution
no code implementations • 17 Apr 2022 • Dung Nguyen, Phuoc Nguyen, Hung Le, Kien Do, Svetha Venkatesh, Truyen Tran
Inspired by the observation that humans often infer the character traits of others, then use it to explain behaviour, we propose a new neural ToM architecture that learns to generate a latent trait vector of an actor from the past trajectories.
Towards Effective and Robust Neural Trojan Defenses via Input Filtering
no code implementations • 24 Feb 2022 • Kien Do, Haripriya Harikumar, Hung Le, Dung Nguyen, Truyen Tran, Santu Rana, Dang Nguyen, Willy Susilo, Svetha Venkatesh
Trojan attacks on deep neural networks are both dangerous and surreptitious.
Episodic Policy Gradient Training
1 code implementation • 3 Dec 2021 • Hung Le, Majid Abdolshah, Thommen K. George, Kien Do, Dung Nguyen, Svetha Venkatesh
We introduce a novel training procedure for policy gradient methods wherein episodic memory is used to optimize the hyperparameters of reinforcement learning algorithms on-the-fly.
Semantic Host-free Trojan Attack
no code implementations • 26 Oct 2021 • Haripriya Harikumar, Kien Do, Santu Rana, Sunil Gupta, Svetha Venkatesh
In this paper, we propose a novel host-free Trojan attack with triggers that are fixed in the semantic space but not necessarily in the pixel space.
Clustering by Maximizing Mutual Information Across Views
no code implementations • ICCV 2021 • Kien Do, Truyen Tran, Svetha Venkatesh
We propose a novel framework for image clustering that incorporates joint representation learning and clustering.
Semi-Supervised Learning with Variational Bayesian Inference and Maximum Uncertainty Regularization
1 code implementation • 3 Dec 2020 • Kien Do, Truyen Tran, Svetha Venkatesh
We propose two generic methods for improving semi-supervised learning (SSL).
Unsupervised Anomaly Detection on Temporal Multiway Data
no code implementations • 20 Sep 2020 • Duc Nguyen, Phuoc Nguyen, Kien Do, Santu Rana, Sunil Gupta, Truyen Tran
These include the capacity of the compact matrix LSTM to compress noisy data near perfectly, making the strategy of compressing-decompressing data ill-suited for anomaly detection under the noise.
Theory and Evaluation Metrics for Learning Disentangled Representations
2 code implementations • ICLR 2020 • Kien Do, Truyen Tran
We make two theoretical contributions to disentanglement learning by (a) defining precise semantics of disentangled representations, and (b) establishing robust metrics for evaluation.
Graph Transformation Policy Network for Chemical Reaction Prediction
no code implementations • 22 Dec 2018 • Kien Do, Truyen Tran, Svetha Venkatesh
We address a fundamental problem in chemistry known as chemical reaction product prediction.
Attentional Multilabel Learning over Graphs: A Message Passing Approach
no code implementations • 1 Apr 2018 • Kien Do, Truyen Tran, Thin Nguyen, Svetha Venkatesh
GAML regards labels as auxiliary nodes and models them in conjunction with the input graph.
DeepProcess: Supporting business process execution using a MANN-based recommender system
1 code implementation • 3 Feb 2018 • Asjad Khan, Hung Le, Kien Do, Truyen Tran, Aditya Ghose, Hoa Dam, Renuka Sindhgatta
Process-aware Recommender systems can provide critical decision support functionality to aid business process execution by recommending what actions to take next.
Knowledge Graph Embedding with Multiple Relation Projections
no code implementations • 26 Jan 2018 • Kien Do, Truyen Tran, Svetha Venkatesh
Knowledge graphs contain rich relational structures of the world, and thus complement data-driven machine learning in heterogeneous data.
Learning Deep Matrix Representations
no code implementations • 4 Mar 2017 • Kien Do, Truyen Tran, Svetha Venkatesh
We derive several new deep networks: (i) feed-forward nets that map an input matrix into an output matrix, (ii) recurrent nets which map a sequence of input matrices into a sequence of output matrices.
Multilevel Anomaly Detection for Mixed Data
no code implementations • 20 Oct 2016 • Kien Do, Truyen Tran, Svetha Venkatesh
We propose MIXMAD, which stands for MIXed data Multilevel Anomaly Detection, an ensemble method that estimates the sparse regions across multiple levels of abstraction of mixed data.
Outlier Detection on Mixed-Type Data: An Energy-based Approach
1 code implementation • 17 Aug 2016 • Kien Do, Truyen Tran, Dinh Phung, Svetha Venkatesh
We evaluate the proposed method on synthetic and real-world datasets and demonstrate that (a) a proper handling mixed-types is necessary in outlier detection, and (b) free-energy of Mv. RBM is a powerful and efficient outlier scoring method, which is highly competitive against state-of-the-arts.